Award-winning Paper Questions ECG As Secure Biometric

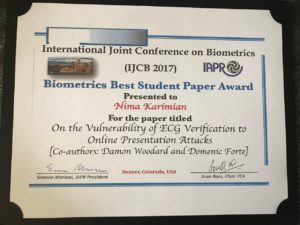
A paper from UConn fourth year PhD student Nima Karimian has won the best student paper award at the recent IJCB 2017 conference in Denver.
The Conference
The International Joint Conference on Biometrics (IJCB 2017) combines two major biometrics research annual conferences, the Biometrics Theory, Applications and Systems (BTAS) conference and the International Conference on Biometrics (ICB). The blending of these two conferences in 2017 is through special agreement between the IEEE Biometrics Council and the IAPR TC-4, and presents an exciting event for the entire worldwide biometrics research community.
The Paper
The paper, “On the Vulnerability of ECG Verification to Online Presentation Attacks,” examined the use of Electrocardiogram (ECG) as a secure biometric modality. ECG has long been regarded as a biometric modality which is impractical to copy, clone, or spoof. However, it was recently shown that an ECG signal can be replayed from arbitrary waveform generators, computer sound cards, or off-the-shelf audio players. The award-winning paper is one of the first in the field to seriously question the security of ECG verification, and goes a long way towards debunking the assumption of its security.
The paper developed a novel presentation attack where a short template of the victim’s ECG is captured by an attacker and used to map the attacker’s ECG into the victim’s, which can then be provided to the sensor using one of the above sources. The authors’ approach involved exploiting ECG models, characterizing the differences between ECG signals, and developing mapping functions that transform any ECG into one that closely matches an authentic user’s ECG. Their proposed approach, which can operate online or on-the-fly, is compared with a more ideal offline scenario where the attacker has more time and resources. In the experiments, the offline approach achieved average success rates of 97.43% and 94.17% for non-fiducial and fiducial based ECG authentication. In the online scenario, the performance is degraded by 5.65% for non-fiducial based authentication, but is nearly unaffected for fiducial authentication.
The work was supported by US Army Research Office (ARO) under award number W911NF16-1-0321.

Categories: News
Published: October 17, 2017
Available Archives